News & Events
-

17 December 2025
GMO GlobalSign Wraps 2025 with Breakthroughs in Certificate Lifecycle Automation and Email Trust Solutions
-

28 October 2025
GMO GlobalSign Named Winner of the Coveted Top InfoSec Innovator Awards for 2025
-
07 September 2025
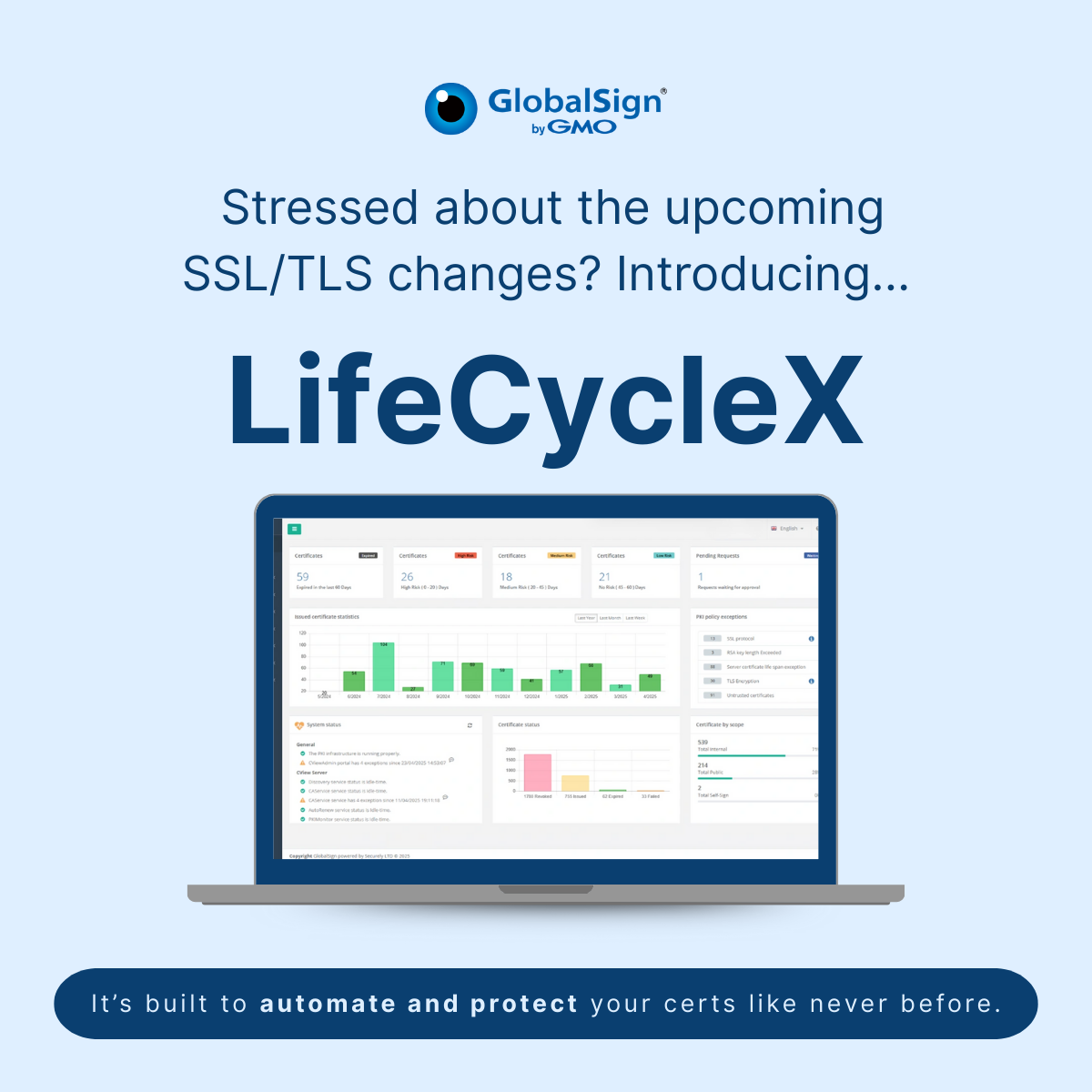
GMO GlobalSign Debuts LifeCycleX for End-to-End Certificate Management and Lifecycle Control
-

05 August 2025
GMO GlobalSign SAN Licensing Supports Businesses
-

22 July 2025
GlobalSign and ID-Security Mark a Decade of Collaboration
-

14 July 2025
GMO GlobalSign Recognized on the Prestigious 2025 MES Midmarket 100 List
back homepage
-

12 November 2019
Top Brazilian Government Website Utilizing GlobalSign for Improved Certificate Vetting
-

15 October 2019
Top Manufacturing Solutions Provider Sanmina Collaborates with GlobalSign for Enhanced Security Protection from Phishing
-
23 July 2019
GlobalSign Launches IoT Developer Program and IoT Developer Portal to Streamline IoT Security Integrations and Accelerate Time to Market
-

12 November 2019
Top Brazilian Government Website Utilizing GlobalSign for Improved Certificate Vetting
-

15 October 2019
Top Manufacturing Solutions Provider Sanmina Collaborates with GlobalSign for Enhanced Security Protection from Phishing
-
23 July 2019
GlobalSign Launches IoT Developer Program and IoT Developer Portal to Streamline IoT Security Integrations and Accelerate Time to Market


