Post Quantum Computing
Future-proofing digital trust with safe certificates
Certificate Authority and Post-Quantum Cryptography Synergy
In an era where technology is rapidly advancing, staying informed about emerging trends that could impact the security of your digital certificates has become essential for Certificate Authority (CA) customers. One such trend is the development of post-quantum computing (PQC), a revolutionary field with the potential to disrupt current cryptographic algorithms. Traditional encryption methods, like RSA and ECC, may become vulnerable in the face of quantum computers, and PQC steps in to provide robust safe certificate solutions.
Post-Quantum-Safe Certificates
As new algorithms draw close to being announced in the wake of quantum challenge, we take a look at what certificates could look like in the post quantum world.
|
 |
|---|---|
| Root CA and Intermediate CA | Leaf/End Entity Certificates |
|
These certificates follow the same structure and key usages that we currently know and understand. The main difference is the key types as illustrated below: Currently dilithium3 is used for the Root and the Intermediate CA. This algorithm was selected in 2022 by NIST for Digital Signatures, so it's likely it'll be an option for TLS/x509 certificates. Once finalized, it is likely to be known as ML-DSA-65 once FIPS 203. This is just in relation to Digital Signature PQ-Safe algorithms, in order for the whole TLS handshake to be fully PQ-Safe, the Key Exchange algorithms also need to be updated which is likely to use Kyber. |
These are the types of certificates which people are most familiar with, as these are issued to those who want to secure their websites. Requesting a Leaf or End Entity certificate will function similarly to the Certificate Signing Requests (CSR) we use today, containing the SubjectDN (the common_name and any organization details) and Subject Alternative Names,which is a list of the resources that the SSL / TLS certificate is intended to secure, i.e. a domain name or IP address. However when requesting a PQ-Safe cert, compared to current certificate options, a CSR or ACME request will need to have a PQ-Safe key type, such as Dilithium2. |
can be found here
Certificate Status Checks
A PKI/Certificate Authority infrastructure provides two ways to check if a certificate has been revoked, namely OCSP and CRL, which work in slightly different ways. As we are planning for when traditional key types are no longer secure, these methods for communicating if certificates have been revoked will also need updating to use PQ-safe. Otherwise, malicious parties could try to falsely prove that valid certificates have been revoked or erase the revocation of certificates which should no longer be trusted.
Our Commitment to Your Security
At GlobalSign we're committed to staying ahead of the curve when it comes to cryptographic advancements. Our dedicated team is actively involved in PQC research and development, ensuring that your digital certificates remain secure in the face of emerging quantum threats.
What do you need to do?
The realization of quantum computing-driven IT systems may still be some years away but it’s something to consider now as you work to improve your crypto-agility levels today and for tomorrow.
- Have an inventory of your certificates and keys
- Identify and address any vulnerabilities
- Develop a plan to replace vulnerable certificates and keys quickly
- Maintain up-to-date ownership information
- Automate management
The Origins of Quantum Computing
The origins of quantum computing can be traced back to the early 20th century when several groundbreaking discoveries in the field of quantum mechanics laid the foundation for this novel approach to computation. Key scientists, such as Max Planck, Albert Einstein, and Niels Bohr, contributed to the development of quantum mechanics, which would later provide the principles for quantum computing.
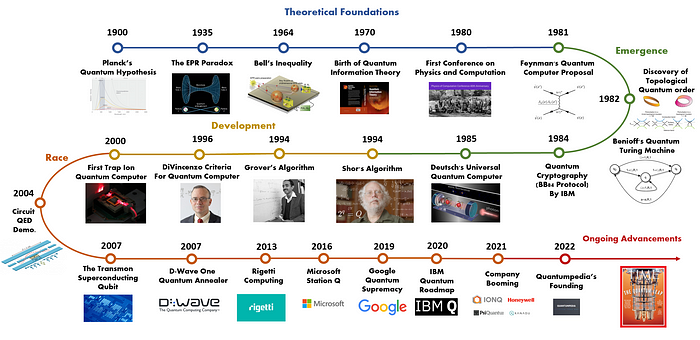
Source: Quantumpedia

Post-Quantum Computing and Your Certificate Authority
In this informative eBook, we delve into the concerns surrounding PQC and provide clarity on why CA customers need not worry about its implications on the security of their certificates. Join us as we navigate the evolving landscape of digital security and reassure you about the robustness of our certificate services in the face of emerging challenges.
Read nowGet in touch with us
Contact us today for your PKI needs and have a trusted partner to ensure you are crypto agile.

