The (evolving) requirements for S/MIME and the attempt to create a standard
As you might know, public-trusted Certificate Authorities (CAs) must meet strict requirements to qualify as (and remain) publicly trusted. There are many stakeholders besides the CAs themselves; everybody wants to ensure that practices for certificate issuance are secure and PKI can continue to play a fundamental role in security on the world wide web. One of the most important bodies governing the requirements that CAs must meet is the CA/Browser Forum (CA/B Forum) and its dedicated working groups. The CA/B Forum working groups have published the official requirements for publicly trusted SSL/TLS and code signing certificates for quite a while already. It is imperative for CAs to be following those requirements – otherwise the public trust can be easily lost.
And then there are S/MIME certificates. These have been gaining more and more commercial relevance in recent years and many large companies have started to leverage publicly trusted S/MIME certificates for signing and encrypting their email. Due to lack of industry standards and guidance, CAs and email client applications have started to set their own rules for certificate profiles and content, some of which conflict with each other. To resolve this issue, the S/MIME working group under the CA/B Forum was established. The working group is looking to standardize certificate profiles which would be more uniformly accepted, leading to wider interoperability.
Changing times
One key standard that is being discussed is the validity period of S/MIME certificates – in fact, some email clients are already requiring a shorter validity period (see figure from Google below). In the past few years, the maximum allowed certificate validity for SSL/TLS has been reduced from 5 years to 3 years to 13 months – a change which is generally recognized as very beneficial in terms of overall security.
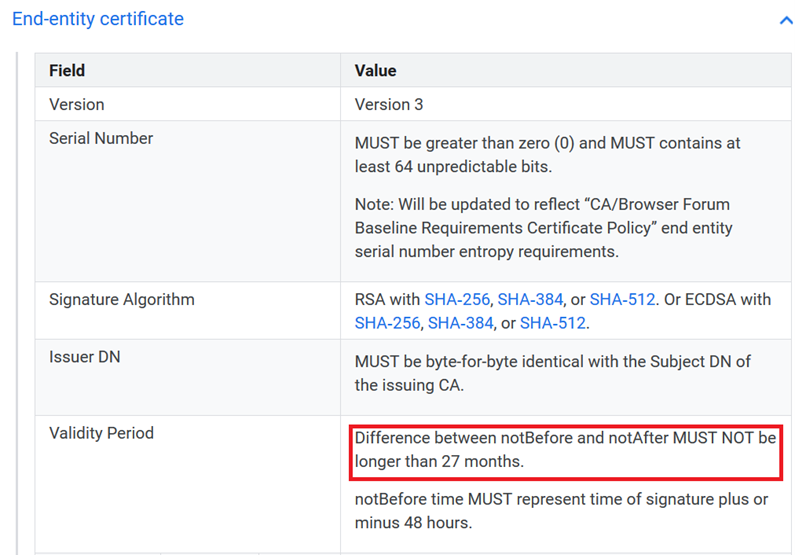
Image source: https://support.google.com/a/answer/7300887#zippy=%2Cend-entity-certificate
At this point, it’s important to clarify: Shorter validity periods for certificates is a practice we, at GlobalSign, totally agree with. There is a general argument that can be made in favour of shorter validity periods. Shorter certificate validity periods boost “crypto-agility.” Put simply, more frequent exchange of key material means more frequent mitigation of cryptographic weaknesses and less impact of key compromise.
However, in contrast to SSL/TLS, automated enrollment for S/MIME certificates does not see the same level of support that ACME for SSL/TLS does, just to give one example. Also, a full roll-out of S/MIME certificates across an enterprise typically means installation and configuration on many more devices than SSL/TLS certificates. Administrators therefore benefit from longer validity periods since they can reduce effort in manually supporting certificate renewal – that’s one argument for a “longer” validity period.
How would these evolving standards affect customers? And where do we go from here?
GlobalSign is represented in the aforementioned CA/B Forum working group for S/MIME and actively trying to shape a standard for S/MIME certificates everybody can agree on. At the same time, GlobalSign is continuously innovating when it comes to supporting certificate lifecycle management in the enterprise. GlobalSign’s Certificate Automation Manager takes away much of the “manual” effort in S/MIME certificate renewal and therefore perfectly supports our vision for shorter validity periods for S/MIME and other types of certificates.
For the time being: Consider purchasing S/MIME certificates with a maximum validity of 825 days (approximately 27 months) if trust by ALL email clients is what matters to you most. If you are not yet ready for automating your certificate lifecycle management and want to reduce manual overhead on renewal as much as possible, there is no need to worry. For the foreseeable future, we will continue offering S/MIME certificates with a validity of 3 years. Regardless of what changes arise in the next several years (and arise they will), rest assured that we at GlobalSign will be glad to assist you in future-proofing your business with crypto-agile solutions you can trust.
Ready to become crypto-agile? Connect with our experts today!
Editor’s Note: This blog was originally published in April 2021 but has since been reviewed to ensure that the content is in line with industry standards, regulations and insights.






