In the ever-evolving landscape of technology, staying ahead of the curve is essential for organizations striving to excel. Enter G-Cloud 13, the latest iteration of the game-changing UK government procurement framework. This blog post takes you on a journey through the world of G-Cloud 13, unveiling its features, benefits, and how it can revolutionize the way government businesses operate.
What is G-Cloud 13?
G-Cloud, shorthand for "Government Cloud," is a pioneering initiative by the UK government that enables public sector organizations to procure cloud-based services and solutions from pre-vetted suppliers. With G-Cloud 13, this initiative has reached new heights, offering an even wider array of services to drive innovation, streamline processes, and elevate the public sector's capabilities.
Key Features of G-Cloud 13
- Expanded Service Categories: G-Cloud 13 encompasses an extensive spectrum of service categories, ranging from cloud hosting and software, to support and consultancy services. This expansion ensures that organizations can find tailored solutions to meet their unique requirements.
- Enhanced Supplier Network: The framework boasts an enriched pool of suppliers, including both established players and innovative startups. This diversity empowers buyers to find the perfect match for their projects, fostering healthy competition and driving quality up while keeping costs in check.
- Simplified Procurement: G-Cloud 13 leverages a user-friendly digital marketplace, making the procurement process swift, transparent, and straightforward. This streamlining of procurement procedures saves time, reduces administrative burdens, and enhances overall efficiency.
- Focus on Security and Compliance: Security and data protection are paramount. G-Cloud 13 maintains rigorous standards for suppliers, ensuring that all offerings adhere to stringent security and compliance requirements. This provides peace of mind for organizations dealing with sensitive data.
Let’s look at an example
A government agency is responsible for managing sensitive citizen data, including tax records, social security information, and personal identification data. They recognize the critical need to enhance data security and protect this sensitive information from unauthorized access and cyber threats.
The government agency turns to G-Cloud services to implement a robust Public Key Infrastructure (PKI) solution. Here's how they proceed:
1. Supplier Selection
The agency reviews the list of G-Cloud-approved suppliers specializing in PKI solutions. They choose a supplier with a proven track record in providing PKI services, ensuring that the solution aligns with their security requirements.
2. Digital Identity Issuance
The PKI solution facilitates the issuance of digital identities to citizens and government employees. Everyone receives a digital certificate that includes a public key for encryption and a private key for decryption. These certificates are stored securely in a centralized directory managed by the PKI system.
3. Secure Communication Channels
With their digital identities, government employees can securely communicate and exchange sensitive information over encrypted channels. This ensures that any data transferred between agencies or to citizens remains confidential and protected from eavesdropping.
4. Two-Factor Authentication (2FA)
The PKI solution supports two-factor authentication, where individuals need both their digital certificates and a separate authentication factor (such as a smart card or biometric verification) to access government systems. This adds an extra layer of security to prevent unauthorized access.
5. Data Signing and Authentication
The agency utilizes the PKI solution to digitally sign important documents and transactions, providing a tamper-evident record of the transaction's authenticity. This is crucial for legal and regulatory purposes.
6. Revocation and Key Management
The PKI solution includes mechanisms for revoking compromised or expired certificates. Additionally, it manages the lifecycle of cryptographic keys, ensuring that keys are generated, stored, and replaced securely.
Implementing a PKI solution through G-Cloud services brings numerous advantages to the government agency, including:
- Enhanced Data Security: The agency achieves a higher level of data protection through strong encryption and secure authentication mechanisms
- Regulatory Compliance: The digital signatures provided by the PKI solution ensure compliance with legal and regulatory requirements for secure document signing
- Mitigation of Cyber Threats: The robust authentication and encryption mechanisms offered by the PKI solution reduce the risk of cyber-attacks and data breaches
- Streamlined Operations: Secure digital communication and authentication lead to more efficient government processes and services
- Trusted Framework: Leveraging G-Cloud-approved PKI services ensures that the solution adheres to stringent security and compliance standards
This example highlights how a government agency can leverage G-Cloud services to implement a PKI solution that enhances data security, authentication, and document integrity. By using digital identities and encryption, the agency not only safeguards sensitive information but also establishes a secure framework for communication and transactions. G-Cloud's emphasis on security and compliance ensures that the implemented PKI solution aligns with the agency's needs and regulatory requirements.
Closing Thoughts
G-Cloud 13 is more than a procurement framework; it's a gateway to innovation, collaboration, and efficiency. By providing access to an array of cutting-edge cloud services, it empowers public sector organizations to stay competitive in a rapidly evolving digital landscape. As we embrace the possibilities of G-Cloud 13, we pave the way for a brighter and more technologically advanced future.
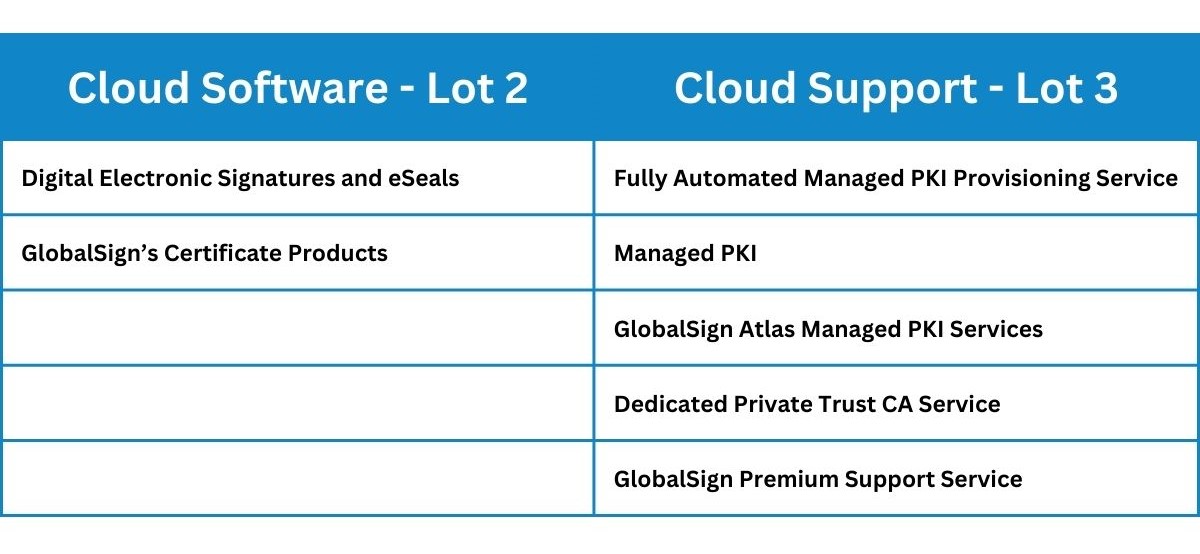
To find out more about the G-Cloud 13 services provided, click here.
GlobalSign provides PKI and online identity protection services giving enterprises a platform to manage internal and external identities. Our solutions allow organizations to deploy secure e-services including SSL / TLS, email and document signing. We automate PKI deployments for users, mobiles, and machines allowing for complete visibility, cost, and time efficiency.