Hackers. They’re quite a unique bunch. And, naturally, given their chosen line of work they have decided to take advantage of the Coronavirus. It’s a sad state of affairs, but really, is anyone surprised? We’re not.
That being said, hackers are exploring every angle to wreak havoc and possibly make a buck. Here are three ways.
Target #1: The Healthcare Industry
One of the first and most concerning attacks was on the US Health and Human Services Department. The attack supposedly involved a campaign of disruption and disinformation that was aimed at undermining the response to the coronavirus pandemic. It is also alleged it may have been the work of a foreign actor, but that has not been confirmed.
According to research from Atlas VPN, 83% of healthcare systems are running on outdated software. The company based part of its findings on a Palo Alto Networks survey of 1.2 million Internet of Things (IoT) devices used in thousands of healthcare organizations across the US. The survey found that 56% of devices were still running on the Windows 7 operating system, which Microsoft stopped supporting in January of this year. Worse, the research also revealed that 27% of medical devices are still operating on Windows XP – which Microsoft hasn’t supported since April of 2014. And it’s the healthcare industry. That’s deeply concerning.
In addition, due to COVID-19, hospitals are now using patient monitoring devices more than ever. Since research shows that one-in-four such devices have security issues, Atlas VPN predicts that cybercriminals will be focusing on the healthcare sector in 2020.
Target #2: Anyone with Email
Phishing emails attempt to steal passwords and personal information – or even conduct espionage operations by hackers working for nation-states.
As WIRED magazine stated in their article Coronavirus Sets the Stage for Hacking Mayhem, phishing and scam websites themed around the pandemic are exploding on the web. Some reports estimate thousands of new domains are cropping up every day. To make matters worse, the story continues, “Home Wi-Fi often doesn't have the same defenses—think firewalls and anomaly detection monitoring—of corporate environments. And it doesn't help that some leading corporate VPNs have major vulnerabilities that companies don't always take the time to patch.”
Remember, if an email sounds too good to be true, it probably is. And if the message in an email demands money or some other type of urgent action, take a moment to be certain it is truly legitimate. Look for red flags like vague subject lines, incorrect use of grammar, lack of personalization and more.
Enterprises might want to take this time to invest in an email security solution. Digitally signed, S/MIME encrypted emails are one of the best ways to help employees differentiate legitimate emails from phishing attempts.
Want some more tips on spotting phishing emails? This post has some terrific information.
Target #3: Android Users
A new Android app claims to provide users access to a virus-tracking map. However, what really happens is the user is downloading ransomware.
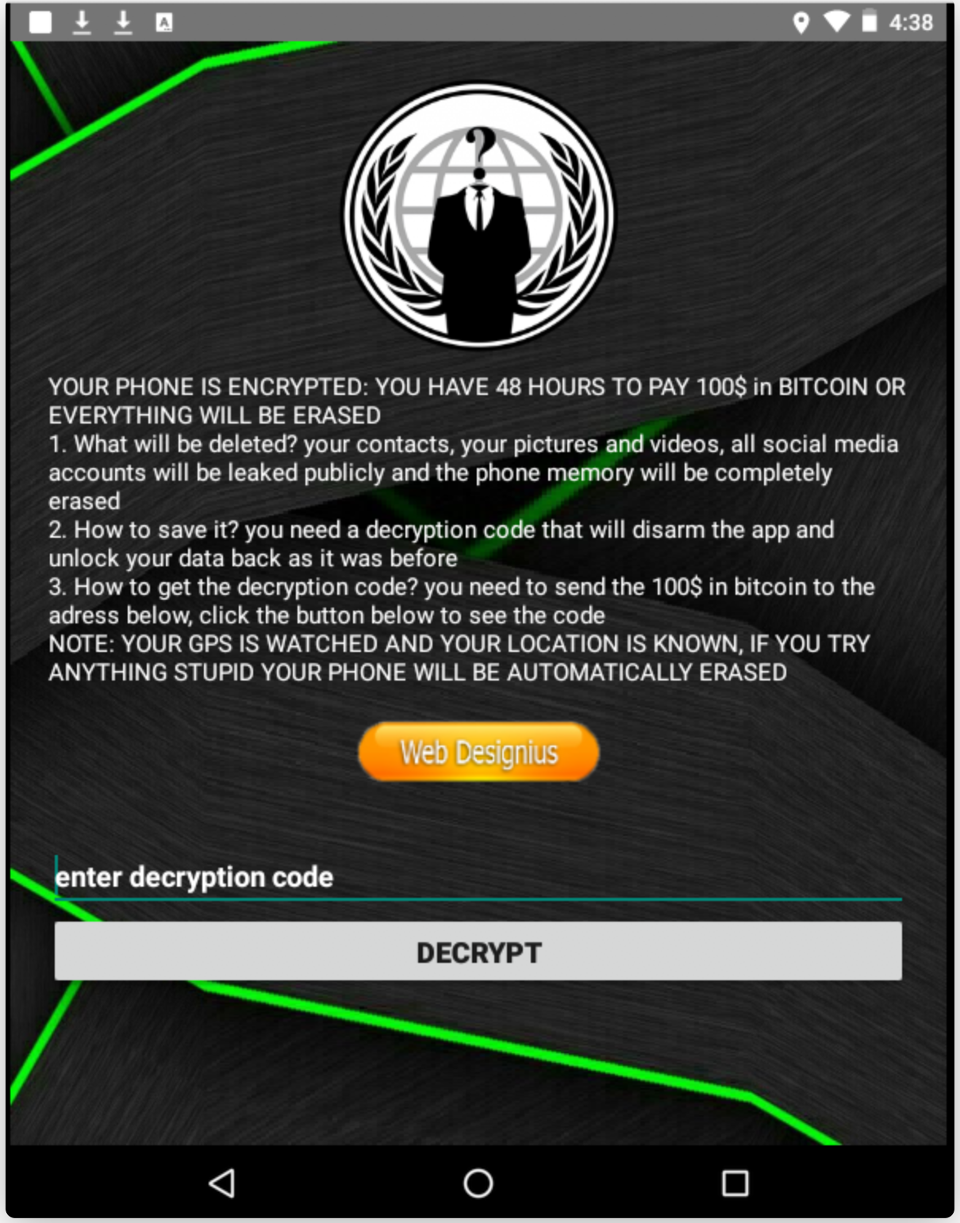
Image Source: Forbes
A team of researchers at DomainTools discovered the malicious app. Aptly named Covid Lock, a domain will prompt users to download the app to a Coronavirus tracker, but what ends up happening is the victim is locked out of their phone by forcing them to change their password. The demand for ransom – about $100 in Bitcoin – follows in this technique known as a screen-lock attack.
Per Forbes, the DomainTools research team explains that “the coronavirusapp[.]site domain initially contained an iframe sourcing directly from infection2020.com (a website from an independent developer for tracking U.S.-based COVID-19 news) and a small banner above that encouraged the installation of the malicious application.”
The article continues with recommendations such as downloading apps directly from the Android Play Store, which is being cleaned up to ensure there aren’t any malicious apps. In addition, don’t follow links or open COVID-19 attachments unless you are ABSOLUTELY certain the source is legitimate.
On the Bright Side, Some Hackers May Ease Up During COVID-19
Despite all the bad news, perhaps there’s a ray of light in terms of cyber attacks.

Image Source: BleepingComputer
Last week, Lawrence Abrams, the creater and owner of BleepingComputer, contacted well known ransomware groups about their thoughts on the coronavirus. He asked them a million dollar question: Would they continue to target health and medical organizations during the COVID-19 pandemic? As of the morning of Thursday, March 19th, two had replied to Abrams. One attacker behind the DoppelPaymer ransomware threat, said they "always try to avoid hospitals, nursing homes." In addition, when they do attack local government targets, they "do not touch 911," (or so they claim). But the attacker also said that sometimes emergency communications are hit due to network misconfigurations.
A second group that Abrams reached was the operators of the Maze ransomware threat. They told him they would stop attacking medical organizations until “the stabilization of the situation with the virus.”
Of course, there are still other hacking groups that will to continue to do the dirty work and wreak havoc worldwide. Still, it’s heartening to know that, some hackers, somewhere, appear to have a heart. And maybe love their grandmas enough to take a break. For a little while anyway.







