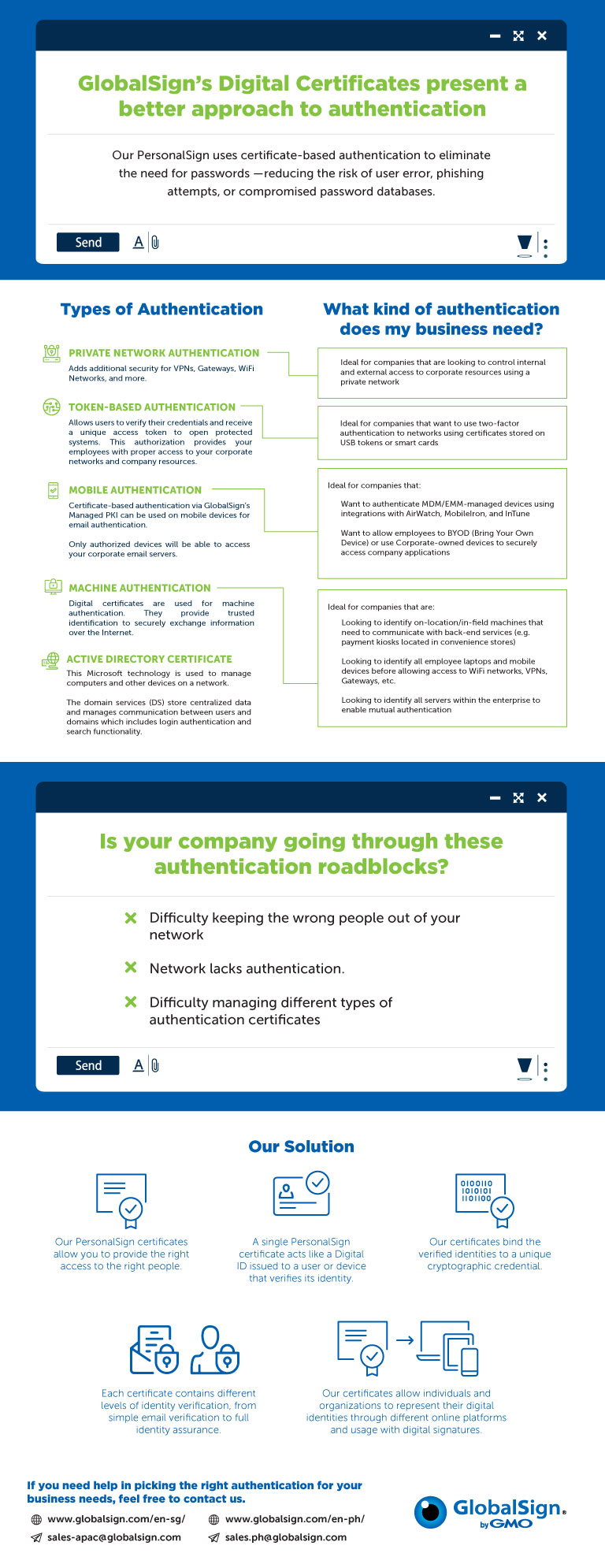
With the increase in cases of data breaches and identity theft, the sole reliance on traditional single-factor authentication, SFA (username and password) is not enough to protect your online accounts and data. Two-factor authentication (2FA) has become the norm when it comes to secure access. Nowadays, businesses have been deploying 2FA to control who can access their organizations’ networks and resources. Learn more about authentication, the different types of authentication solutions you can deploy, and how to choose the right one for your business.