Editor's Note: This blog was originally published in April of 2017 and has been recently updated.
Ever landed on a website and received an error like this?
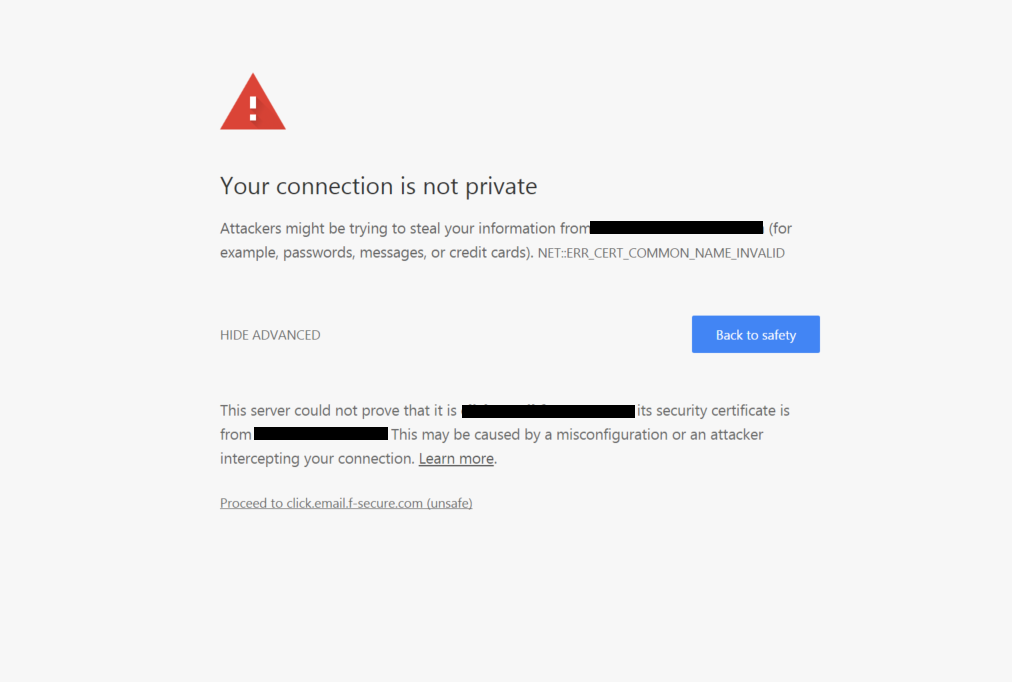
Chrome: ‘This server could not prove that it is example.com; its security certificate is from example.com. This may cause a misconfiguration or an attacker intercepting your connection’
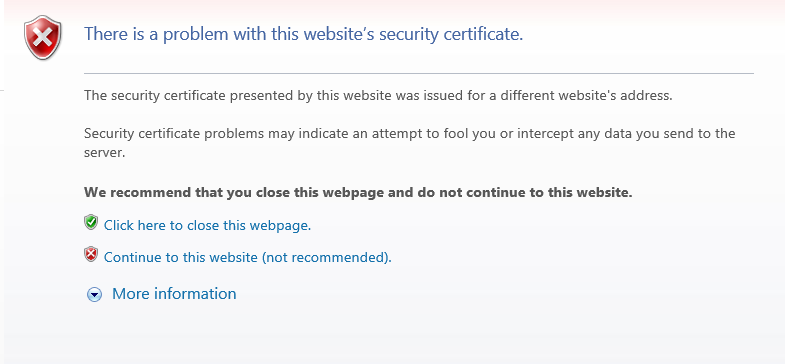
Internet Explorer: ‘The security certificate presented by this website was issues for a different website’s address. Security certificate problems may indicate an attempt to fool you or intercept any data you send to the server.’
There are several different ways this can be presented, depending on the browser and the version of the browser you are using. Whether you are a website visitor or the website owner, though, an error like this isn’t something you want to see!
So let’s just start by explaining what this error means.
A common name mismatch error occurs when the common name or SAN of your SSL/TLS Certificate does not match the domain or address bar in the browser. This can happen simply by visiting https://example.com instead of https://www.example.com if the certificate does not have them both listed in the SAN of the certificate.
First things first, if you are not the website owner, you need to get in touch with someone who can fix the issue. DO NOT go ahead and continue anyway. It is quite possible that the error is showing because a hacker or phisher is trying to pass an impostor website off as the website you are trying to visit.
If you own the website or domain and you want to resolve this error, here are some tips to follow:
How to Solve a Common Name Mismatch Error
You could be having this issue for several reasons, so you should start with a thorough analysis. Start by entering the domain of your website into GlobalSign’s SSL checker.
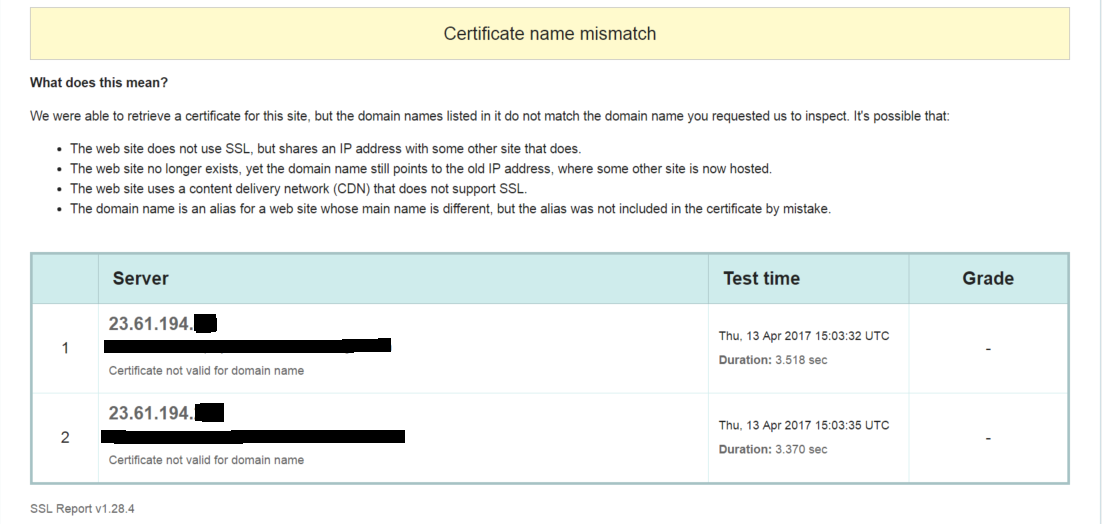
Figure 1 Results of using SSL Checker on Website with Mismatch Error
The first thing to look for when doing this check is to find out what certificate is currently configured to a domain or IP address on the server. This will normally help you identify why you are getting the error, as there can be quite a few reasons.
The main thing to remember is there is nothing wrong with the SSL/TLS Certificate or with your website per se. At some point between someone visiting a domain and someone reaching your website, the wrong certificate is being presented.
You may need to contact your IT department to find out where the certificate was installed and where it is being configured.
The website address was not included in your common name by mistake
It might be as simple as the example mentioned above. You have purchased a certificate with the common name www.example.com, but not added example.com as a SAN to the certificate.
Make sure you click 'Ignore Certificate Mismatch' in the GlobalSign SSL Checker and it will take you to a full analysis of the SSL/TLS Certificate on that domain. You can see from the Common Name and SAN section if the correct domains and IPs are included.
Figure 2 Results when you follow 'Ignore Certificate Mismatch' and inspect the full certificate
When you order a certificate from GlobalSign with your common name as www.example.com, we will give you example.com for free if you validate on example.com. If you put example.com as your common name, we have a UC SAN option so you can add www.example.com for free during your ordering process. You can also add it after issuance by editing your SAN options.
The website does not use SSL but shares an IP address with a site that does
If your website is sharing an IP address with other sites, this may or may not matter and solutions may vary.
You may be on a shared host. Some hosting companies require a dedicated IP address to support SSL. If one of the customers sharing that IP address has installed an SSL/TLS Certificate on that shared IP, it could interfere with the other sites.
It could also be that the client connecting or the server hosting (or both) do not support Server Name Indication (SNI).
An example of this would be if you have example.com (default site) and example.org hosted on the same IP. You have certificates for both and they are both configured. If the server does not support SNI, only the default SSL Certificate will be served up. If the client does not support SNI, they will only see the default site’s certificate.
If the server and client support SNI, the correct certificate is served up each time. Pretty much all modern clients and servers support SNI but it can cause issues with legacy systems.
So as a solution, you may have to support SNI or get a dedicated IP (which involves DNS settings changes).
The website no longer exists, yet the domain name still points to the old IP address, where some other site is now hosted
DNS settings will help you here as well. Make sure the DNS is pointing to the new IP not the old one!
The hosting provider you go with has pre-configured settings which override your certificate installation
Your hosting provider may have some settings pre-configured which force SSL on each of their domains. If you purchase an SSL/TLS Certificate from another third-party Certificate Authority and install it, you will see a mismatch error.
Like above, go to ‘Ignore Certificate Mismatch’ in the GlobalSign SSL Checker to see the full certificate details. If the common name or SAN includes the name of your hosting provider, this is probably what is happening.
You need to contact your hosting provider and have them remove their certificate so you can install yours. If they say they will not do this – switch hosting providers as this is bad practice. You should be able to get an SSL/TLS Certificate from wherever you want.
Configurations of your server or firewall
You should pay attention to your firewall and load balancer settings. A firewall in particular can be set to grab a certificate from one server even though it points to multiple servers, so you need to make sure this is set-up correctly.
Sadly, in this situation, you are the only one who can fix the issue and should have some IT knowledge or at least, have someone hired who can help you with IT.
Summary
In summary, it’s important to get all the information correct during the ordering process and have your server set-up and configured properly. If you aren’t sure about how to add a SAN or include your base domain in the ordering process, give us a call today.
If you think the issue lies with your server configurations, you should talk to your IT team or hosting company.





